Back in February 2011, Rick Redman from Korelogic came to present his Supercharged Password Cracking Techniques at the Austin OWASP chapter monthly meeting.
With these techniques, he was able to crack large password database in a very short time using a tool called John The Ripper. In this article, I want to present what are these techniques and what we can do to secure our identities online.
In December 2010, the media group Gawker (Gizmodo.com, Lifehacker.com) was attacked and their 750,000-password database was stolen. The passwords were encrypted with the algorithm DES, but it did not prevent them from being cracked. More recently, the Sony's Playstation Network was also being attacked. More than 75 million passwords, emails, credit card numbers and other personal data have been compromised.
 |
|
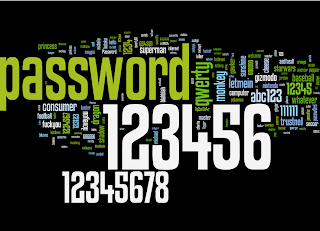
These decrypted real user passwords not only revealed what are the commonly used passwords but also showed that many people are using the same patterns to build their passwords. Knowing these patterns, it is possible to crack passwords in a much shorter time than using a basic brute force technique.
Here is how you can customize John The Ripper (JTR) to crack encrypted passwords. Please note that I am using an unofficial build of JTR available here. First, you need to create a file containing the passwords to crack. In our example, this file is called pwd2crack.txt and here is the file content:
user1:d0763edaa9d9bd2a9516280e9044d885 user2:a8e003b1180fd689f558657079d05f5aThe file contains the passwords for 2 users: user1 and user2. The passwords are hashed using the MD5 algorithm.
To run John The Ripper, you can use the following command:
>john --wordlist=password.lst --format=raw-MD5 pwd2crack.txt Loaded 2 password hashes with no different salts (Raw MD5 [raw-md5 SSE2 16x4]) monkey (user1) guesses: 1 time: 0:00:00:00 100.00% (ETA: Mon May 2 22:42:22 2011) c/s: 469428 trying: trinity - halloAs you can see, JTR was able to crack user1's password almost instantly because "monkey" was in its list of passwords. But JTR was unable to crack user2's password. You can try the default command using the built-in logic to guess the passwords.
>john --format=raw-MD5 pwd2crack.txt Loaded 2 password hashes with no different salts (Raw MD5 [raw-md5 SSE2 16x4]) Remaining 1 password hash guesses: 0 time: 0:00:00:04 (3) c/s: 195765 trying: 39of - 3ayo guesses: 0 time: 0:00:00:15 (3) c/s: 2965K trying: beteng95 - betel197 guesses: 0 time: 0:00:00:43 (3) c/s: 5430K trying: swoji1x - swojsem guesses: 0 time: 0:00:00:55 (3) c/s: 5817K trying: ahabh9 - ahabu2 guesses: 0 time: 0:00:01:08 (3) c/s: 6052K trying: luk12ay - luk11io Session abortedAfter running this command for a few minutes, my computer got really hot and JTR was still not able to crack user2's password. While JTR is running, press the space bar to print in the console the progress of the operation.
One of the common patterns for password is to add a date at the end of the password, especially the current year. You can configure JTR to use its password dictionary with "2011" at the end of each entry by adding the following to the file john.ini or john.conf.
[List.External:CustomWithYear2011]
void filter() {
/* calculate word length */
int length;
length = 0;
while (word[length]) length++;
word[length] = '2';
word[length+1] = '0';
word[length+2] = '1';
word[length+3] = '1';
word[length+4] = 0;
}
This function, written in C, alters the password to hash before it is compared to the one in pwd2crack.txt. Then you can call JTR with this customization.
>john.exe --format=raw-MD5 --wordlist=password.lst --external=CustomWithYear2011 pwd2crack.txt Loaded 2 password hashes with no different salts (Raw MD5 [raw-md5 SSE2 16x4]) Remaining 1 password hash monkey2011 (user2) guesses: 1 time: 0:00:00:00 100.00% (ETA: Mon May 2 22:06:09 2011) c/s: 25600 trying: freedom2011 - barney2011This time JTR was able to crack the second password: monkey2011.
You can get more details about these techniques on the Korelogic website.
Here are a few tips I would recommend:
- The passwords protecting your most valuable accounts should not be shared with other website
- Use password that are strong and easy to remember
- If available, use 2-factor authentication (eg: Paypal, Google, World of Warcraft)
- Raise your users awareness (password strength indicator, trainings)
- Use a strong hash algorithm to store the passwords (BlowFish)
- Integrate a second factor of authentication
9 comments:
Hi Mat,
How did you get the data you used to generate your cloud?
Thanks,
I found the top 250 most common password cracked from the Gawker database on this blog: http://blog.duosecurity.com/2010/12/brief-analysis-of-the-gawker-password-dump/
Thanks for reading!
Matthias
I found an interesting blog about advanced password cracking techniques: http://reusablesec.blogspot.com/
Here is another interesting link about password cracking with a graphical card:
http://mytechencounters.wordpress.com/2011/04/03/gpu-password-cracking-crack-a-windows-password-using-a-graphic-card/
Here is good analysis about password patterns.
http://www.troyhunt.com/2011/06/brief-sony-password-analysis.html
thank you
XKCD says it all:
"Through 20 years of effort, we've successfully trained everyone to use passwords that are hard for humans to remember, but easy for computers to guess."
http://xkcd.com/936/
Does this work with MS Cache passwords ? Could please let me know the syntax ?
Thanks
@KR
Were able to obtain the password hash from windows? If my memory serves, the Windows algorithm was not supported by the free standard version of JTR, you may check if it is supported by the Pro version. When I tried, I could not find a tool to extract the password on Win7. If you find one, please leave a link here :)
Post a Comment